Threat intelligence is a growing investment priority for businesses and enterprises. According to research from Frost & Sullivan, businesses can improve their security posture by knowing the potential threats and attack vectors, in order to address these in a proactive manner.
“Most of the attacks are voluminous, targeted, multi-vector, polymorphic, signature-less, and importantly unknown; making it challenging for enterprises to prevent these attacks. Hence is the need for a cybersecurity framework that leverages threat intelligence and can identify and respond to advanced threats thereby creating an improved security posture,” writes Rajarshi Dhar, Senior Industry Analyst with Frost & Sullivan’s Information and Communication Technologies Practice.
Breach and attack simulation (BAS) is one of the most viable strategies to ensure cybersecurity amid the rapidly evolving and exponentially increasing cyber attacks on businesses and organizations. However, not all BAS solutions being offered on the market are created equal. They have varying sets of features and functions that create differences in their security validation outcomes. To find the best BAS platform, look for the following features.
1. Ease of use
“Cybersecurity is a problem that every level in an organization faces, one that goes well beyond the purview of a Chief Security Officer,” says Samuel Visner, Senior VP at consulting and technology firm ICF International. Considering how everyone in an organization is already granted access to various IT assets of an organization, it is only logical to get everyone involved in maintaining cybersecurity.
Making it solely the responsibility of the IT department is not only inexpedient but also possibly disastrous. It is important that the centerpiece cybersecurity solution employed by a company is easily comprehensible to all possible users. Being highly technical does not encourage involvement and can even become a major obstacle in enabling cooperation towards a strong security posture.
Not everyone is expected to have access to the BAS platform, but it is advantageous for it to be intuitive and well-organized to make security information analysis and presentations seamless and easy. Likewise, ease of use ensures that it would not take long to onboard new members of the cybersecurity team.
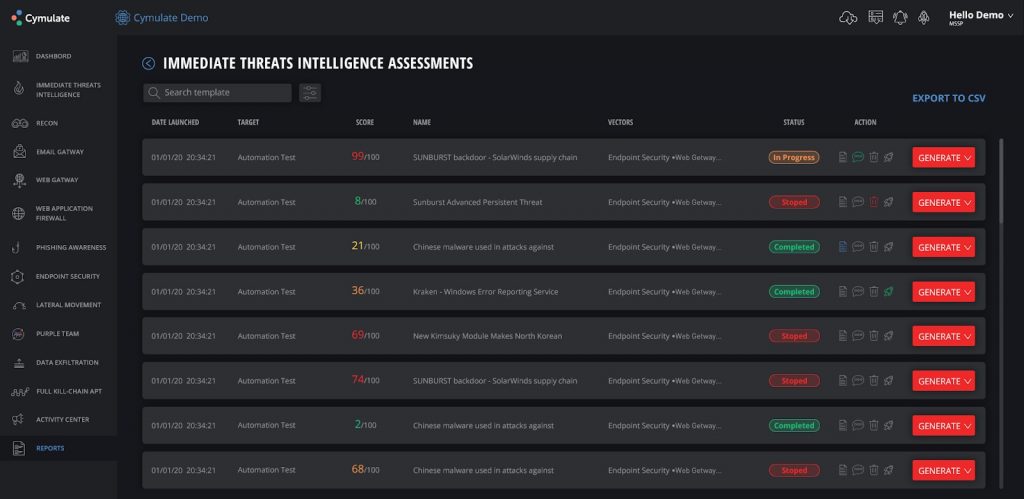
It is preferable to have a BAS platform that makes use of simplified data presentations such as the use of scores and color-coded indicators. Cymulate’s BAS platform employs artificial intelligence to automatically sort threats and provide security control assessment scores to make it easy for users to address the most urgent concerns. Likewise, it helps to have a system that readily presents immediate threat intelligence assessments complete with details on statuses, quick buttons for the possible actions to be taken, and the ability to quickly generate relevant reports.
2. Software-as-a-service
A BAS platform available in a software-as-a-service (SaaS) model provides many advantages. For one, it does not require configuration before or upon deployment. SaaS BAS solutions can be used out-of-the-box just like Cymulate, which provides expert threat intelligence-driven risk evaluations without requiring users to have some degree of technical know-how to tinker with the settings and options.
Another advantage of SaaS solutions is that they do not need maintenance. The software is patched and updated automatically. If there are issues, they will have already been addressed before users learn about them. The service provider is responsible for making sure the software works as intended and that it does not become a source of vulnerabilities or exploitable weaknesses.
Additionally, SaaS breach and attack simulation solutions are arguably the most cost-effective and efficient option for growing companies. They are highly scalable. Regardless of the size or whenever there are changes in an organization, the solution works. Things can be scaled up or down depending on the needs. They are also accessible from anywhere there is internet access. Businesses that expand to new locations do not have to worry about their security validation system being physically bounded. There is no need to move equipment or install client software to the new hardware deployed in the new location.
Moreover, the cost of using SaaS services is typically lower compared to on-premises solutions. They are generally more cost-efficient because of their subscription-based model. Users can upgrade to more features or settle with standard functions under a basic subscription based on what they need. Also, users do not have to invest in new hardware and tediously install the software in the new devices.
Concerns that SaaS solutions may not compare to the performance of client-based platforms are generally baseless. The benefits of SaaS overwhelmingly outweigh the drawbacks, especially when compared to client-based or on-premise solutions.
3. Integration with other security solutions
Organizations that decide to adopt BAS as part of their security posture are certainly going to use several other security solutions. Or they are most likely already using security products from other vendors. As such, it is essential for a BAS platform to be integrable with other security tools or products.
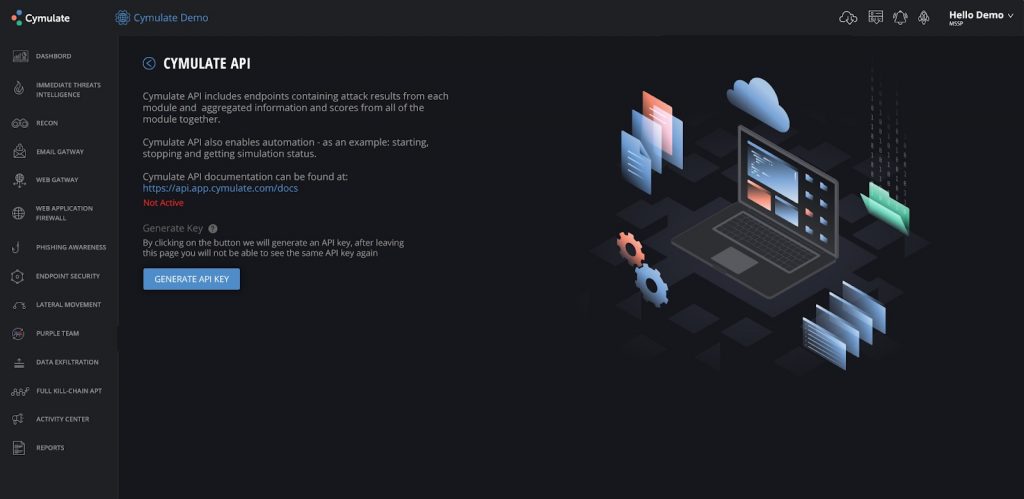
In the case of Cymulate, the platform easily integrates with Microsoft, Rapid 7 Nexpose, Tenable, Qualys, Nexpose, Splunk, IBM Radar, and other security solutions. It also provides an API that seamlessly presents attack simulation results from different modules and aggregates various security information and test scores. The API also allows users to automate certain processes including the initiation, stopping, and updating of simulation statuses.
4. MITRE ATT&CK operationalization
Started in 2013, MITRE ATT&CK is a globally accessible knowledge base and security validation framework that presents various adversary techniques and tactics as shared by security experts from different parts of the world. It presents matrices that detail the manifestations and processes by which newly discovered attacks go through. In exchange, it facilitates more effective and efficient security testing
MITRE ATT&CK provides a reliable up-to-date source for cyber threat intelligence to help organizations prepare for potential attacks. It aims to acquaint everyone with new adversary tactics and techniques, so they can be more capable of detecting, preventing, or mitigating a cyber attack.
Cymulate operationalizes the MITRE ATT&CK framework to more efficiently spot problems in an organization’s security posture, optimize it, and significantly improve the likelihood of detecting, identifying, and remediating attacks. This framework is by no means perfect, but it has already helped many in maximizing threat detection and prevention facilities.
5. Custom security testing
Lastly, a good BAS platform should make it possible to produce and automate custom security validation exercises based on what a company deems suitable. Organizations rarely share the same needs, wants, and concerns, so it makes sense to undertake bespoke security testing to employ the best possible approaches to unique needs.
Cymulate’s BAS platform is designed to enable and automate red/purple team exercises as well as other security assurance procedures that match real-world situations as observed by the organizations that do the testing themselves. It ensures that security assurance programs match the distinctive security conditions and policies of an organization.
In summary
BAS platforms are useful in ascertaining that security controls are working as they should. However, users should bear in mind that approaches in breach and attack simulations vary from one vendor or platform to another. To find the BAS platform that can deliver the best outcomes, looking for the features described above would be a good start.
The preferable BAS platform is one that is easy to use, integrable with other security products, and capable of undertaking custom security testing. It is also highly advantageous to choose a SaaS platform because of its scalability, relatively maintenance-free operation, and typically lower initial and operating costs. Additionally, it is a plus point if a breach and attack platform takes advantage of the MITRE ATT&CK framework.