This post will explain web security testing. The software industry has achieved a strong acknowledgement at this age. Nevertheless, in the current years, the cyber-world seems to be a much more dominating and driving force shaping up the new kinds of nearly every business. Website-based ERP systems used today are the best proof that IT has revolutionized our precious global village.
Nowadays, websites are not implied just for publicity or marketing; however, these have been developed into more powerful tools to deal with total company requirements.
What Is Web Security Testing Complete Guide
In this artilce. you can know about web security testing here are the details below;
Companies are not just utilizing Web-based Payroll systems, Shopping Malls, Banking, and Stock Trade applications; however, they are likewise being offered as products today.
This means that online applications have gotten customers and users’ trust regarding their crucial feature called SECURITY.
No doubt, the security factors is of primary worth for desktop applications too.
Nevertheless, when we discuss the web, the value of Security increases greatly. If an online system can not secure the deal data, nobody will ever think about using it. Security is neither a word in search of its meaning yet, nor is it a subtle idea. Nevertheless, I want to list some compliments on Security.
Examples of Security defects in an application.
- – A Student Management Systems is insecure if the ‘Admission’ branch can modify the data of the ‘Exam’ branch.
- – An ERP system is not protected if DEO (data entry operator) can create ‘Reports’.
- – An online Shopping Malls has no security if the consumer’s Credit Card Detail is not secured.
- – A custom-made software application have inadequate Security if an SQL inquiry obtains real passwords of its users.
Security.
Now, I provide to you the simplest meaning of Security in my own words.
” Security indicates that authorized gain access to is approved to protected data and unauthorized access to is limited”.
It has two major elements; initially, the defence of information and the second one is access to that data. Additionally, whether the application is desktop or web-based, Security focuses on the two previously mentioned elements.
Let us have an overviews of security aspects for both desktop and web-based software application applications.
Desktop And Web Security Testing.
A desktop application needs to be secure not only concerning its access; however, likewise concerning the company and storage of its information.
Similarly, web application demands a lot more, Security concerning its gain access to information protection. A web designer should make the application immune to SQL Injections, Brute Force Attacks and XSS (cross-site scripting). Similarly, if the web application helps with remote access points, then these need to be secure. You can also check another post like free cad software.
Furthermore, bear in mind that Brute Force Attack is not just related to web applications; desktop software is likewise vulnerable to this.
I hope this foreword suffices, and now let me come to the point. Kindly accept my apology if you up until now thought that you are reading about the subject of this short article. Though I have quickly described software application Security and its significant concerns, my topic is ‘Security Testing’.
I will now describe how security functions are implemented in software application and how must these be evaluated. My focus will be on the Whats and Hows of security testing, not of Security.
Recommended Security Testing Tools.
# 1) Netsparker.
Netsparker is a web app security testing solution with automated crawling and scanning for all types of tradition & modern-day web applications such as HTML5, Web 2.0, and Single Page Applications. It utilizes Proof-Based Scanning Technology and scalable scanning representatives.
It offers you total visibility, although you have a large number of possessions to manage. It has many more performances, like team managements and vulnerability management. It can be integrated into the CI/CD platforms like an Jenkins, TeamCity, or Bamboo.
# 2) Kiuwan.
Discover and fix vulnerabilities in your code at every phase of the SDLC.
Kiuwan is compliant with the most strict security requirements consisting of OWASP, CWE, SANS 25, HIPPA, and more. Incorporate Kiuwan in your IDE for immediate feedback throughout advancement. Kiuwan supports all significant programming languages and integrates with leading DevOps tools.
# 3) Indusface WAS Free Website Malware Check.
Indusface WAS supplies both manual Penetration testing bundled with its own automatic web application vulnerability scanner that finds and reports vulnerabilities based upon OWASP leading ten and consists of a Website reputation check of links, malwares, and defacement checks of the website in every scan.
List Of Top 8 Security Testing Techniques.
# 1) Access to Application.

Whether it is a desktop app or a site, access security is implemented by ‘Roles and Rights Management. It is frequently done implicitly while covering performance,
For Example, in a Hospitals Management System, a receptionist is least concerned about the lab tests as his task is to just sign up the clients and arrange their consultations with physicians.
So, all the menus, types and screens connected to lab tests will not be readily available to the ‘Receptionist’ role. Hence, the appropriate implementation of functions and rights will guarantee the Security of gain access to.
The tester ought to develop numerous user accounts with various in addition to several roles. Then he needs to use the application with the help of these accounts and must validate that every function has access to its modules, screens, kinds, and menus only. If the tester finds any conflict, he ought to log a security problem with total confidence.
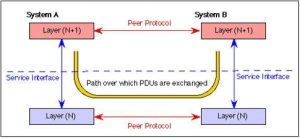
This can also be comprehended as authentication and permission screening which is very magnificently illustrated in the below image:
So, essentially, you need to test about ‘who you are’ and ‘what you can do’ for unique users.
A few authentication tests include a test for password quality rules, a test for default logins, a test for password recovery, test captcha, test for logout performance, a test for password change, a test for security question/answer, etc.
Similarly, some of the permission tests consist of a test for course traversal, a test for missing out on authorization, a test for horizontal gain access to control issues, etc.
# 2) Data Protection.

There are three aspects of information security. The first ones is that a user can see or make use of just the information he is supposed to utilize. Functions and rights likewise guarantee this.
For Example, the TSR (telesales representative) of a business can see the data of readily available stock but can not see how much basic material was acquired for production.
So, this element of security testing is currently described above. The 2nd aspect of data security is connected to how that data is stored in the DB. Also check another post like task management software.
Further reading =>> What is Database Security Testing.
All the delicate data need to be secured to make it protect. File encryption ought to be strong, especially for sensitive information like passwords of user accounts, credit card numbers or other business-critical details.
Third and the last element is an extension of this 2nd aspect. Correct security measures should be adopted when the flow of delicate or business-critical data takes place. Whether this information floats in between various modules of the same application or is transferred to various applications, it needs to be encrypted to keep it safe.
How to Test Data Protection: The tester should query the database for ‘passwords’ of the user’s account, billing information of clients, other business-critical and sensitive information and ought to verify that all such information is the conserved encrypted form in the DB.
Similarly, he needs to verify that information is transmitted between different types or screens after correcting only encryption. Additionally, the tester should make sure that the encrypted information is properly decrypted at the destination. Special attention needs to be paid to various ‘send’ actions.
The tester needs to verify that when the info is being transferred between the customer and server, it is not shown in the address bar of a web browser in an understandable format. If any of these verifications stop working, then the application has a security flaw.
The tester must also check for appropriate salting use (adding an extra secret worth to the end input like password and thus making it more powerful and more difficult to be split).
Insecure randomness should likewise be tested as it is a sort of vulnerability. Another way to check data protection is to look for weak algorithm usage.
For Example, since HTTP is a clears text procedure, if sensitive information like user credentials are transferred utilizing HTTP, it is a danger to application security. Instead of HTTP, delicate data should be moved via HTTPS (protected through SSL, TLS tunnel).
However, HTTPS increases the attack surface area, and therefore it needs to be evaluated that server configurations are proper and certificate credibility is ensured.
# 3) Brute-Force Attack.

Some software application tools mostly make strength Attack. The idea is that by utilizing a legitimate user ID, the software attempts to guess the associated password by attempting to log in again and again.
A simple example of Security versus such an attack is account suspension for a brief period as all the mailing apps like ‘Yahoo’, ‘Gmail’ and ‘Hotmail’ do. If a particular number of consecutive efforts (mostly 3) stop working on logging ineffectively, that account is obstructed for a long time (30 minutes to 24 hrs).
How to evaluate Brute-Force Attack: The tester should confirm that some account suspension system is readily available and is working accurately. (S) He needs to log in with void user IDs and Passwords to ensure that the software application obstructs the accounts if continuous attempts are made to login with void credentials.
If the application is doing so, it is safe and secure against brute-force attack. Otherwises, this security vulnerability must be reported by the tester.
Evaluating for strength can likewise be divided into two parts– black box screening and grey-box testing.
In Black box testing, the authentication approach used by the application is found and tested. The grey box testing is based on partial knowledge of password & accounts details and memory compromise attacks.
Click on this link to explore black box & grey box brute force testing along with examples.
The above three security aspects need to be considered for web and desktop applications, while the following points relate to web-based applications only.
# 4) SQL Injection And XSS (Cross-Site Scripting).

Conceptually speaking, the themes of both these hacking efforts is comparable, so these are discussed together. In this approach, the destructive script is utilized by hackers to manipulate a website.
There are some methods to immune against such efforts. For all input fields of the site, field lengths must be specified little enough to restrict any script’s input.
For instance, The Last Name needs to have a field length of 30 instead of 255. There may be some input fields where big data input is needed. For such fields, appropriate recognition of input should be performed before conserving that data in the application.
Furthermore, in such fields, any HTML tags or script tag input must be restricted. To provoke XSS attacks, the application needs to dispose of script reroutes from unknown or untrusted applications.
How to test SQL Injection and XSS: Testers must ensure that optimum lengths of all input fields are specified and implemented. (S) He must also guarantee that the specified length of input fields does not accommodate any script input in addition to tag input. Both these can be easily evaluated.
For instance, If 20 is the optimum length defined for the ‘Name’ field and the input string.”
thequickbrownfoxjumpsoverthelazydog” can validate both these restrictions.
It must also be verified by the tester that the application does not support confidential access approaches. In case any of these vulnerabilities exist, the app remains at risk.
Generally, SQL injection testing can be done through the following five methods.
- – Detection techniques.
- – Standard SQL injection techniques.
- – Fingerprint the database.
- – Exploitation Techniques.
- – SQL Injection Signature Invasion Techniques.
Click on this link to read in detail about the above methods to test SQL injection.
XSS is likewise a type of injection which injects destructive script into a site. Click here to explore extensive screening for XSS.
# 5) Service Access Points (Sealed And Secure Open).
Today, companies depend on and work together with each other, and the very same holds good for applications, especially sites. In such a case, both the partners should specify and release some gain access to points for each other.
Until now,, the scenario seems rather basic and simple, but, for some web-based items like stock trading, things are not easy and simple.
When there is a great deal of the target audience, access to points needs to be open adequate to help with all users, accommodating enough to fulfil all users’ demands and protect enough to manage any security-trial.
How to Test Service Access Points: Let me explains it with the Example of the stock trading web application; a financier (who wants to buy the shares) ought to access present and historical data on stock rates. The user should be offered the centre to download this historical information. This requires that the application should be open enough.
By accommodating and protected, I suggest that the application facilitate investors to trade freely (under the legislative guidelines). They might acquire or sale 24/7, and the information of deals need to be immune to any hacking attack.
Furthermore, many users will be engaging with the application concurrently, so the application should supply enough access to indicate entertainment to all users.
Sometimes, these access points can be sealed for unwanted applications or people. This depends upon the business domain of the application and its users.
For instance, A custom-made web-based Office Management System might acknowledge its users based on IP Addresses and rejects to develop a connection with all other systems (applications) that do not fall in the ranges of valid IPs for that application.
The tester must make sure that all the inter-network and intra-network access to the application rely on applications, machines (IPs) and users.
To verify that an open access points is secure enough, the tester needs to try to access it from different makers having both relied on on and untrusted IP addresses. Different sorts of real-time deals need to be attempted in bulk to have great confidence in the application’s performance. By doing so, the capacity of access points of the app will also be observed plainly.
The tester needs to guarantee that the application captivates all the communication requests from relied on IPs and applications only while all the other demands are declined.
Similarly, if the app has some open access point, then the tester needs to guarantee that it enables (if required) the uploading of information by users in a safe method. In this safe and secure method, I suggest the file size limitation, file type limitation, and scanning of the uploaded apply for infections or other security risks.
This is all how an tester can verify the Security of an app with respect to its gain access to points.
# 6) Session Management.

A web session is a sequences of the HTTP request and response transactions related to the exact same user. The session management tests check how sessions management is managed in the web app.
You can check for session expiration after specific idle time, session termination after optimum lifetime, session termination afters log out, check for session cookie scope and period, screening if a single user can have multiple simultaneous sessions, etc.
# 7) Error handling.

Checking for Error handling consists of.
Look for mistake codes: For Example, test 408 demand time-out, 400 bad demands, 404 not discovered, and so on. To check these, you require to make sure demands to the page such that these mistake codes are returned. You can also check another post about voxal voice changer.
The mistake codes are returned with an in-depth message. These messages should not contain many important details that can be utilized for hacking purpose.
Look for stack traces: It essentially consists of giving some exceptional input to the application such that the returned mistake message consists of stack traces that have interesting info for hackers.



